Today’s Cybersecurity Dilemma: Analyzing over 100,000 security incidents daily from more than 150 distinct threat actors
The Challenges:
- Security teams struggle to keep up with threats
- Uncertainty about relevant and significant threats
- Blind spots from ineffective, scattered cybersecurity tools

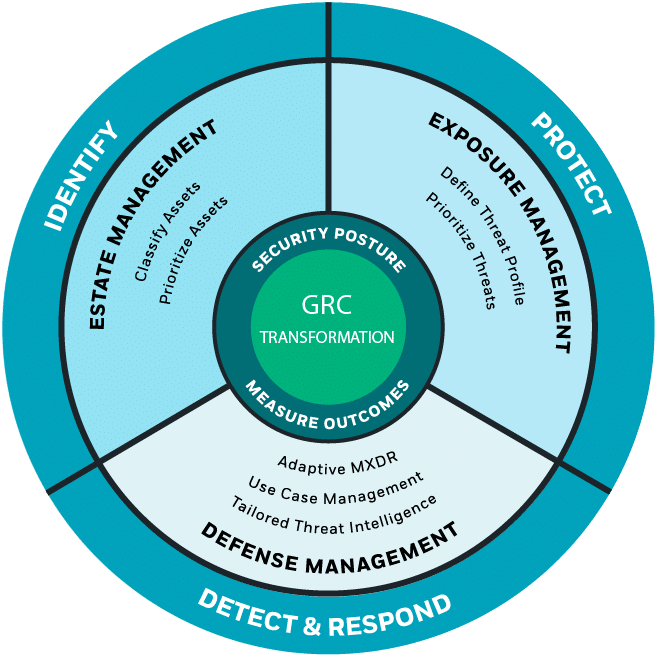
The Solution: Defend Against the Threats That Matter Most
CyberProof provides an integrated threat-led platform that combines:
- Estate (Asset) Management: Tag, classify, and prioritize known and unknown assets to understand your exposure – continuously
- Exposure Management: Focus on relevant threats using CTEM and ASCA frameworks – continuously
- Defense Management: Optimize detection and response playbooks – continuously
- Resulting in GRC Transformation: Mitigate Global Risk, Define Business Outcomes & ROI, Mature Security Posture
SecOps & Risk Mitigation
CyberProof uses OSINT and threat intelligence feeds for visibility into threats.
CyberProof’s adaptable playbooks address continuously evolving threats with updated strategies.
Professionals manage sophisticated networks, leveraging experience to counter advanced threats.
Professionals manage sophisticated networks, leveraging experience to counter advanced threats.
24/7 global SOC support ensures incident response with guaranteed SLA.
24/7 global SOC support ensures incident response with guaranteed SLA.
CyberProof develops recovery plans, restoring capabilities after a cyber incident.
Classify and manage enterprise assets, understanding risks and data sensitivity.
Non-destructive tests uncover potential exploits in assets and applications.
Mitigate security issues early with CyberProof’s training and awareness programs.
Rigorous security assessment for on-premise and cloud applications to ensure protection.
IAM manages user access, monitors for anomalies, ensuring security.
Cloud First approach ensures compliance and security within cloud environments.
Managed service for SIEM, EDR, MXDR, and threat intelligence solutions.
Identify, assess, and mitigate security vulnerabilities through regular scanning.
Partners
“Today I have complete visibility into the entire environment, in real time”
Jamil Farshchi | Equifax CISO
CyberProof CTEM
CyberProof’s CTEM platform, powered by Interpres, is able to continuously identify, assess, and prioritize risk, while enhancing defense services like MDR, Vulnerability Management and Use Case Management to address evolving threats. Take proactive steps to fortify your security today!
Threat Alerts
Secure AI Development Environments — MCP Inspector Flaw Highlights Supply Chain Risks
Researchers have issued a warning about the potential for full system compromise through a vulnerability in Anthropic’s MCP Inspector tool — a popular open-source utility used by developers to test Model Context Protocol (MCP) servers. While a patch is available, this case highlights a wider risk: attackers can abuse poorly secured developer tools, local proxies, and open ports to escalate from simple web-based lures to full remote code execution.
Organizations adopting AI tools, agentic applications, or MCP frameworks should treat local development and testing environments as part of their attack surface. Validate that any MCP Inspector installations are updated to version 0.14.1 or later, review exposed network interfaces, restrict CORS settings, and apply strict least privilege. This serves as a broader reminder that open-source AI integration tools can introduce overlooked supply chain threats if not deployed securely.
Microsoft Patches 130 Vulnerabilities in July Update With Critical RCE and Zero Day
Microsoft’s July 2025 Patch Tuesday fixes 130 vulnerabilities, including 14 critical and 41 remote code execution flaws. Notably, it includes a publicly disclosed zero-day, CVE-2025-49719 (CVSS 7.5), an information disclosure bug in SQL Server that allows unauthenticated access to uninitialized memory over the network. Although exploitation is rated as “less likely,” the early disclosure increases risk. The most critical flaw, CVE-2025-47981 (CVSS 9.8), is a pre-authentication RCE in the Windows NEGOEX mechanism, posing a high risk of wormable attacks similar to WannaCry.
Other major fixes include RCE vulnerabilities in Microsoft Office and SharePoint (CVE-2025-49695 to CVE-2025-49704) and critical issues in Windows KDC Proxy, Connected Devices Platform, and Hyper-V components.