Healthcare, Medical Services and Pharmacies
Mitigating the risk of attack in the healthcare sector
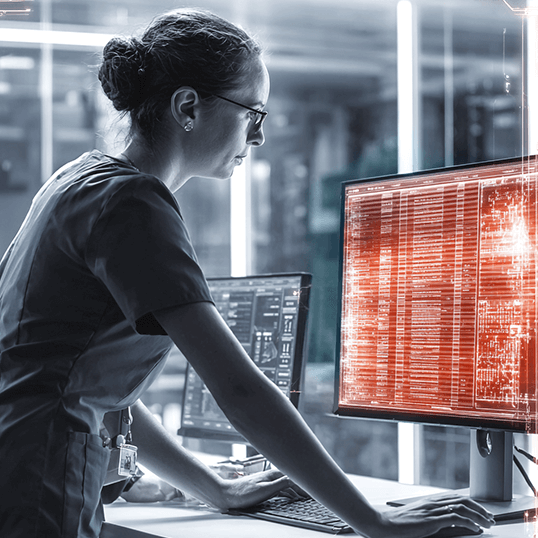
Healthcare organizations are increasingly at risk from cyber attack, often targeted by ransomware attacks, which can bring critical systems to a halt and cause significant disruption to patient care.

Recognized as industry leaders
Which cyber threats are most dangerous to your operations?
Hospitals and other healthcare organizations are responsible for protecting patient data, including personally identifiable information (PII) and protected health information (PHI), which are highly valuable targets for cybercriminals. They frequently need to contend with the use of outdated or unsupported software that can easily be exploited by cybercriminals. Moreover, healthcare organizations work extensively with third-party vendors who have access to patient data and thereby increase the attack surface beyond the perimeter of the organization.
Mitigating risk keeps your people and data healthy

Cloud-native & hybrid deployment
providing greater operational efficiency, with cloud-native tools and automations accelerating detection & response
Reduced time to respond
with orchestration and automation capabilities that provide faster time to response and increased threat landscape visibility

Single view of operations
supporting multi-team SecOps collaboration, with real-time alerts and recommendations for security incidents
Fewer false positives
data and logs are collected from multiple sources, enriching alerts by providing additional context, while reducing errors and time to detect
Leveraging automation to mitigate risk
In an era in which enterprises must maintain multi-cloud environments, automation serves as a critical component – reducing risk while improving efficiency and scalability. Our eBook on “How to leverage automation to mitigate risk” explores the essential components of secure cloud transformation, and how automation can support an efficient and scalable move to the cloud.

Best practices in handling real threat scenarios
SOC L1 and L2, DFIR, Threat Intel, and Threat Hunter teams collaborate to mitigate threats faster and more effectively. Our Cyber Defenders Playbook reviews “lessons learned” by CyberProof’s team to help you improve your detection & response processes.
Improving cyber resilience by leveraging the MITRE ATT&CK
MITRE’s Attacker Tactics, Techniques, and Common Knowledge (ATT&CK) framework is a powerful tool for improving cyber defense. MITRE creates a categorized list of all known attack methods, and connects each attack method with mitigations and detection methods for preventing or identifying attacker techniques.


How to protect your enterprise from cyber threats
DOWNLOAD THE INFOGRAPHIC
Speak with an expert
Discover how we can help you protect patient data by implementing robust measures to identify and mitigate cyber threats.