Manufacturing
Safeguarding critical operations, sensitive data and intellectual property
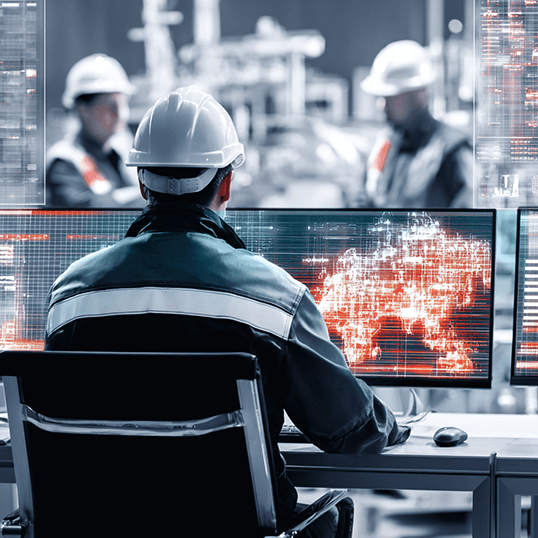
As manufacturers move over to the advanced technologies and interconnected systems that run 24/7, the industry becomes a prime target for cyber threats. In addition to ransomware and supply chain attacks, enterprises are faced with vulnerabilities in industrial control systems (ICS) and intellectual property (IP) theft. Operational downtime resulting from such attacks can cripple manufacturing processes, disrupt supply chains, and lead to significant financial loss.

Recognized as industry leaders
Ensuring continuity of operations
By embracing cybersecurity as an integral part of operations, you can fortify defenses and mitigate the ever-evolving threats in today’s interconnected world. From preventing IP theft to handling supply chain vulnerabilities, CyberProof’s team can support you in anticipating, adapting, and responding to the cyber threats targeting manufacturers with our advanced Managed Detection & Response (MDR) services. Working together with your team in real time, we can help you improve your organization’s security posture to address the growing risk.
Reducing the cybersecurity risks for manufacturers

Cloud-native & hybrid deployment
providing greater operational efficiency, with cloud-native tools and automations accelerating detection & response
Reduced time to respond
with orchestration and automation capabilities that provide faster time to response and increased threat landscape visibility

Single view of operations
supporting multi-team SecOps collaboration, with real-time alerts and recommendations for security incidents
Fewer false positives
data and logs are collected from multiple sources, enriching alerts by providing additional context, while reducing errors and time to detect
Leveraging automation to mitigate risk
In an era in which enterprises must maintain multi-cloud environments, automation serves as a critical component – reducing risk while improving efficiency and scalability. Our eBook on “How to leverage automation to mitigate risk” explores the essential components of secure cloud transformation, and how automation can support an efficient and scalable move to the cloud.

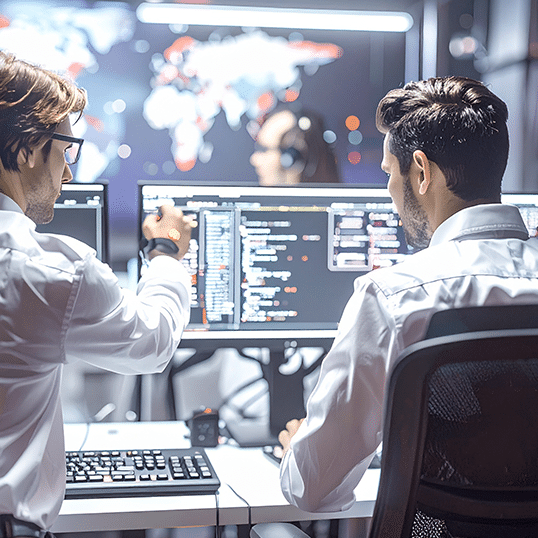
Best practices in handling real threat scenarios
SOC L1 and L2, DFIR, Threat Intel, and Threat Hunter teams collaborate to mitigate threats faster and more effectively. Our Cyber Defenders Playbook reviews “lessons learned” by CyberProof’s team to help you improve your detection & response processes.

Improving cyber resilience by leveraging the MITRE ATT&CK
MITRE’s Attacker Tactics, Techniques, and Common Knowledge (ATT&CK) framework is a powerful tool for improving cyber defense. MITRE creates a categorized list of all known attack methods, and connects each attack method with mitigations and detection methods for preventing or identifying attacker techniques.

Case study: Enabling secure cloud transformation at scale
CyberProof helped a major U.S. industrial supplier scale its security by deploying a next-gen SOC with Microsoft Azure Sentinel, enhancing detection, response, and automation while reducing costs and improving operational efficiency.
Case study: Boosting OT/IoT security and response with Armis
A Fortune 500 manufacturer partnered with CyberProof to improve OT/IoT security, achieving 24×7 MDR, real-time visibility, and a 23% MTTD and 29% MTTR reduction using Armis, CyberProof’s CTEM capabilities, and Google Threat Intelligence.
Speak with an expert
Discover how we can help you safeguard critical operations by implementing robust data protection measures to identify and mitigate cyber threats.